How to Manage CAA Records
Adding a domain you own to your DigitalOcean account lets you manage the domain’s DNS records with the control panel and API. Domains you manage on DigitalOcean integrate with DigitalOcean Load Balancers and Spaces to streamline automatic SSL certificate management.
CAA Record Background Information
Certificate Authority Authorization (CAA) is a standard designed to prevent bad actors from creating unauthorized SSL/TLS certificates. CAA records specify which certificate authorities (CAs) can issue certificates.
Like other types of DNS records, CAA records can apply to an entire domain (like example.com) or to specific subdomains (like assets.example.com). Likewise, you can set the lifespan of the record with a Time To Live (TTL) value given in seconds.
CAA records have three additional fields: tags, values, and flags.
-
Tags are ASCII strings. The CAA standard defines three tags. In addition to these, the CAA standard permits CAs to define their own tags. Each CAA record is limited to a single tag. The defined tags are:
issueauthorizes a single CA to issue any type of certificate for a specific hostname. To allow multiple CAs to issue certificates, each requires its own record.issuewildauthorizes a single CA to issue a wildcard certificate and only a wildcard certificate for a hostname. Again, to allow multiple CAs to issue certificates, each requires its own record.iodefdefines a URL where a CA can report policy violations. Each contact URL requires its own record.
-
Values are strings associated with tags.
- For the
issueandissuewildtags, you typically set the value to the domain name of the CA being granted permission by the record, such asletsencrypt.org. - For
iodefyou supply a URL where policy violations should be reported. This may be the URL of a service set up specifically for this purpose or amailtoURI, such asmailto:admin@example.com.
- For the
-
Flags are unsigned integers between 0 and 255. Currently this field is used to set an issuer critical flag, which specifies how a CA should behave when it encounters a tag it doesn’t understand.
The default flag is 0. When a CA requests the DNS record to issue a certificate, if there’s a tag that it doesn’t understand and the flag is set to 0, it ignores that specific record and continues to process any additional records.
However, if any record in the response has the issuer critical flag, 128, set and the CA doesn’t understand the tag in that record, then a standards-compliant CA must refuse to issue a certificate.
DigitalOcean DNS does not support the following CAA standard features:
- Blocking anyone from issuing certificates by sending a semicolon (
;) in the value - Allowing name-value tags after the CA name, for example:
letsencrypt.org; abc=cde
You can learn more about the DNS Certification Authority Authorization (CAA) Resource Record in RFC 6844.
Creating CAA Records
You can create a new CAA record from the Networking page. From the control panel, either open the Create menu and click Domains/DNS or click Networking in the left nav.
From the Networking page, click the domain. From the domain’s page, under the Create new record header, click CAA. The CAA tab contains the fields you need to add CAA records.
Create Issue Records
This example creates a record that allows Let’s Encrypt to issue certificates for any hostname at digitalocean.love
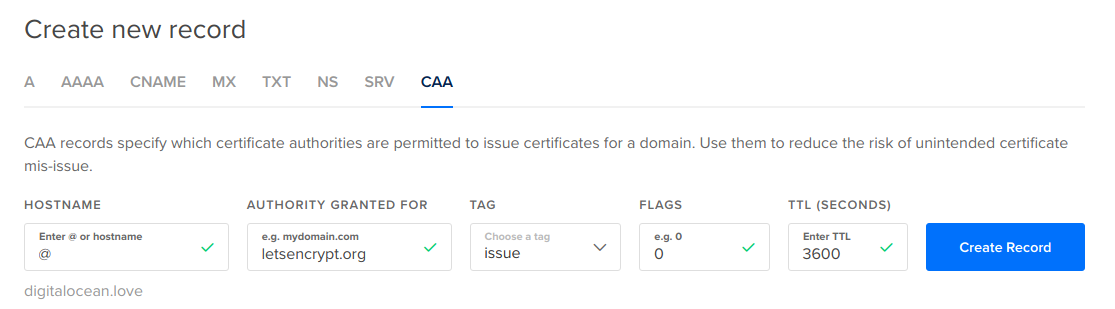
-
HOSTNAME: To apply this record to the entire domain, enter
@. -
AUTHORITY GRANTED FOR: Here, enter the domain name for the Certificate Authority. In this example, that is
letsencrypt.org -
TAG: To give permission for Let’s Encrypt to generate any kind of certificate, select the
issuetag from the dropdown. -
FLAGS: Accept the default of
0. -
TTL (SECONDS): Accept the default of
3600.
Click Create Record. The new CAA record appears at the top of the domain’s record set.
Issue tags are additive. To allow another CA to grant certificates, you need to add an additional record.
Create issuewild Records
Wildcards are a catchall subdomain, like *.digitalocean.love. In the absence of an issuewild record, any CA can issue wildcard certificates. This example adds a record to permit a different certificate authority, Comodo, to issue wildcard certificates (and only wildcard certificates).
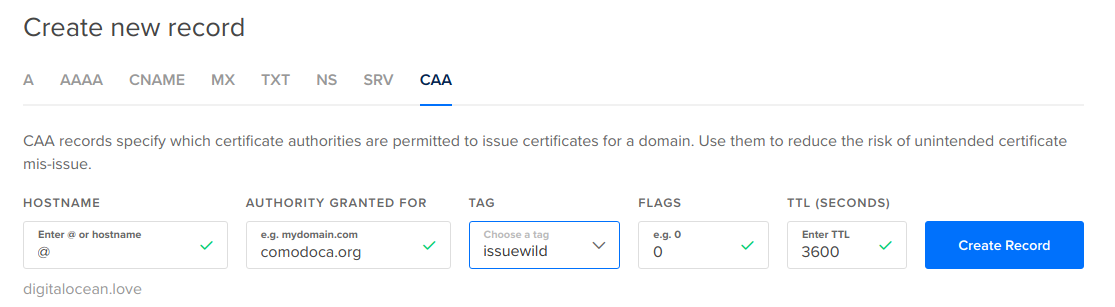
-
HOSTNAME: Apply this to
digitalocean.loveby entering@. -
AUTHORITY GRANTED FOR: Enter Comodo’s domain name,
comodoca.org -
TAG: Select the
issuewildtag from the dropdown. -
FLAGS: Accept the default of
0. -
TTL (SECONDS): Accept the default of
3600.
After adding Comodo, no other CA can issue wildcard certificates unless you add a record that explicitly allows them to.
Create iodef Records
The final piece of this example is adding an iodef record so that CAs have a point of contact in the event of policy violations.
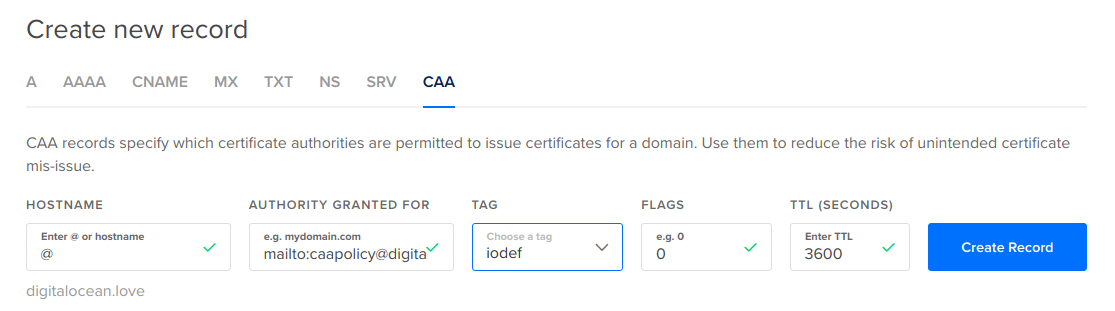
-
HOSTNAME: Enter
@to indicate this contact information is for the entiredigitalocean.lovedomain. -
AUTHORITY GRANTED FOR: Enter the contact email in the format
mailto:caapolicy@digitalocean.love -
TAG: Select the
iodeffrom the dropdown. -
FLAGS: Accept the default of
0. -
TTL (SECONDS): Accept the default of
3600.
If a policy violation occurs, this record lets certificate authorities know whom to contact.